I’m currently studying for Microsoft exam 70-246. I do enjoy studying for exams. It’s hard, but it’s an excellent forcing function. I learn bits and pieces here and there now and then about this and that, but when I have an exam schedule for a set date, I have to study! And not only do I put in more hours, but I follow a more systematic approach. In this article, I’m going to share GreatExam braindumps in case you too are studying and this method works for you.
QUESTION 31
Your company has a private cloud that is managed by using a System Center 2012 infrastructure. You deploy an application visualization solution.
You deploy a server named Server1, and then you install the Remote Desktop Services server role.
Server1 is monitored by using Operations Manager.
You deploy a virtualized application named App1 to Server1.
You need to set the state of Server1 to critical if CPU utilization by App1 exceeds 80 percent for five minutes.
What should you create?
A. a rule
B. a monitor
C. a service level objective (SLO)
D. an event subscription
E. a synthetic transaction
Answer: B
Explanation:
Monitor is the correct answer
Service level Objectives
Service level objectives are measurements to ensure that you are meeting defined service level commitments.
In Operations Manager, you define a service level objective – the set of monitors that you need to track (such as performance or availability) – and then run reports against that service level objective to ensure that you are meeting your goals.
http://technet.microsoft.com/en-us/library/hh212753.aspx
SLO’s are agreed as a means of measuring the performance of the Service Provider.
SLO’s are specific measurable characteristics of the SLA such as availability, throughput, frequency, response time, or quality.
This concept is part of SLM in SCSM 2012.
http://blogs.technet.com/b/privatecloud/archive/2013/03/26/service-manager-2012-and-service-level-management-part-1.aspx
QUESTION STATES:
“You need to set the state of Server1 to critical if CPU utilization by App1 exceeds 80 percent for five minutes.”
SLOs don’t change the state of an object, monitors do:
Create a monitor if…
You want to affect the health of an object.
In addition to generating an alert, a monitor will affect the health state of its target object.
This is displayed in state views and availability reports.
http://technet.microsoft.com/en-us/library/hh457603.aspx
QUESTION 32
Your role of Systems Administrator at ABC.com includes the management of the company’s private cloud.
The company has a System Center 2012 infrastructure that includes System Center 2012 – Service Manager (SCSM).
You use Service Manager for Service Level Management.
You need to create a service level objective (SLO) in Service Manager for incidents that meet the following criteria:
Priority = 1 Incident Category = Email
Problem. Assigned User = Empty.
What should be your first step?
A. You should first create a Service Template.
B. You should first create a Connector.
C. You should first create a Queue.
D. You should first create a Query.
Answer: C
Explanation:
http://blogs.technet.com/b/servicemanager/archive/2012/01/25/scsm-2012-service-level-management.aspx
With queues you can group different work items in Service Manager (SCSM 2010 and SCSM 2012) by criteria. For instance: All Incidents with Priority 2 AND Incident Category „Mail Problem “AND Assigned User is empty.
Queues are used in SCSM 2012 SLA Management to apply the SLA to a group of work items.
SCSM 2012 console -> Library -> Queues”
QUESTION 33
Drag and Drop Questions
Your company has a private cloud that is managed by using a System Center 2012 Operations Manager infrastructure.
The infrastructure contains a management server named Server1.
The network contains two subnets named Subnet1 and Subnet2.
The two subnets are separated by a firewall that prevents ICMP communications.
Server1 is located on Subnet1.
A switch named Switch1 is located on Subnet2.
Switch1 has the following configurations:
– Network ID: 10.10.10.0/24
– IPv4 address: 10.10.10.12
– IPv6 address: fec0:2308::12
You need to discover Switch1.
What should you configure from the Computer and Device Management Wizard? To answer, drag the appropriate values to the correct location in the answer area. (Each value may be used once, more than once, or not at all.)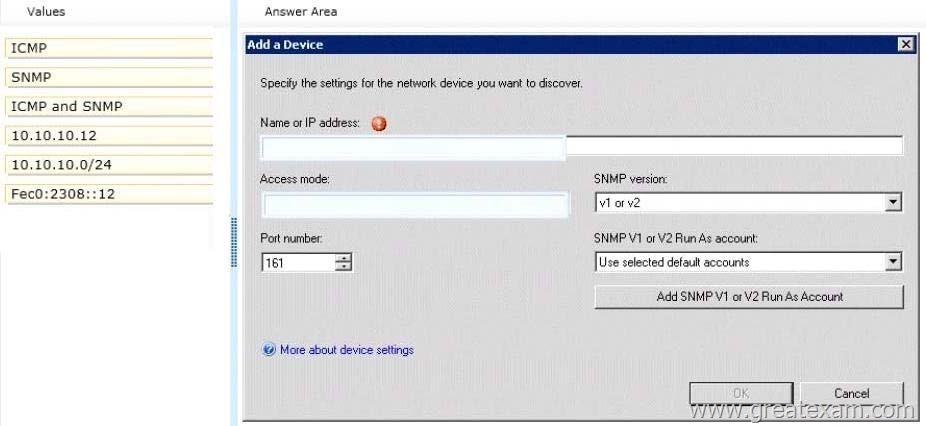
Answer: 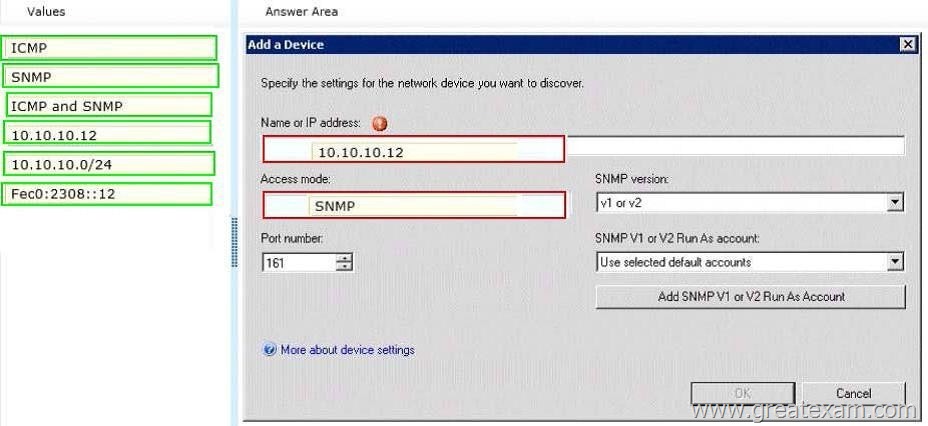
Explanation:
Explicit discovery – An explicit discovery rule will only attempt to discover those devices that you explicitly specify in the wizard by IP address or FQDN.
It will only monitor those devices that it can successfully access.
The rule will attempt to access the device by using ICMP, SNMP, or both depending on the configuration of the rule.
http://technet.microsoft.com/en-us/library/hh212935.aspx
QUESTION 34
Hotspot Questions
Your company help desk uses System Center 2012 Service Manager to manage and track problems.
You need to ensure that the manager of the help desk is notified automatically when a high-priority incident is updated.
What should you configure? To answer, select the appropriate configuration in the answer area.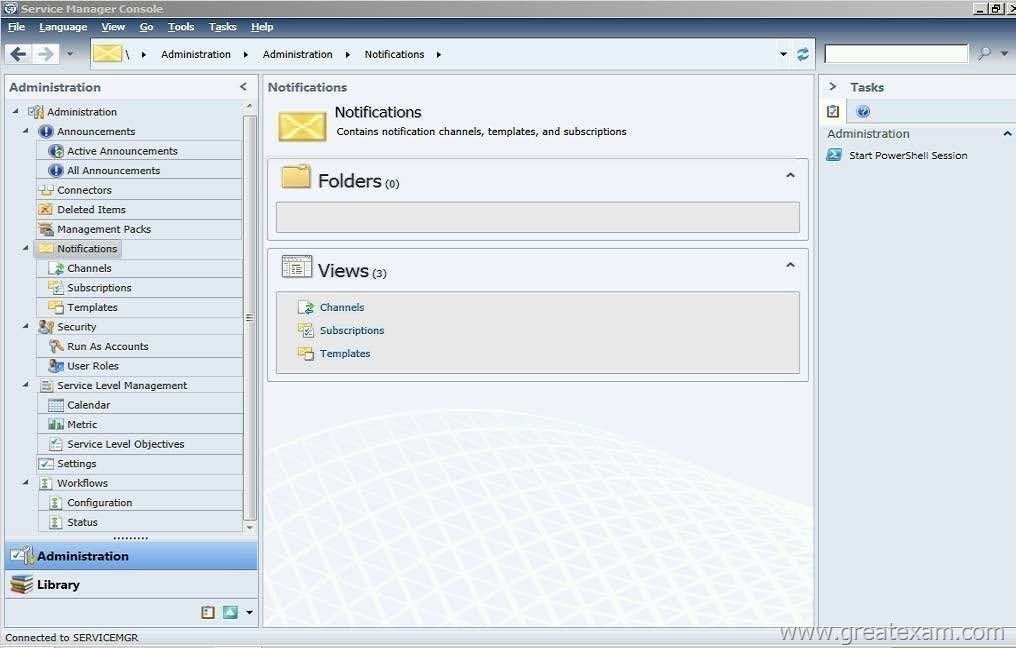
Answer: 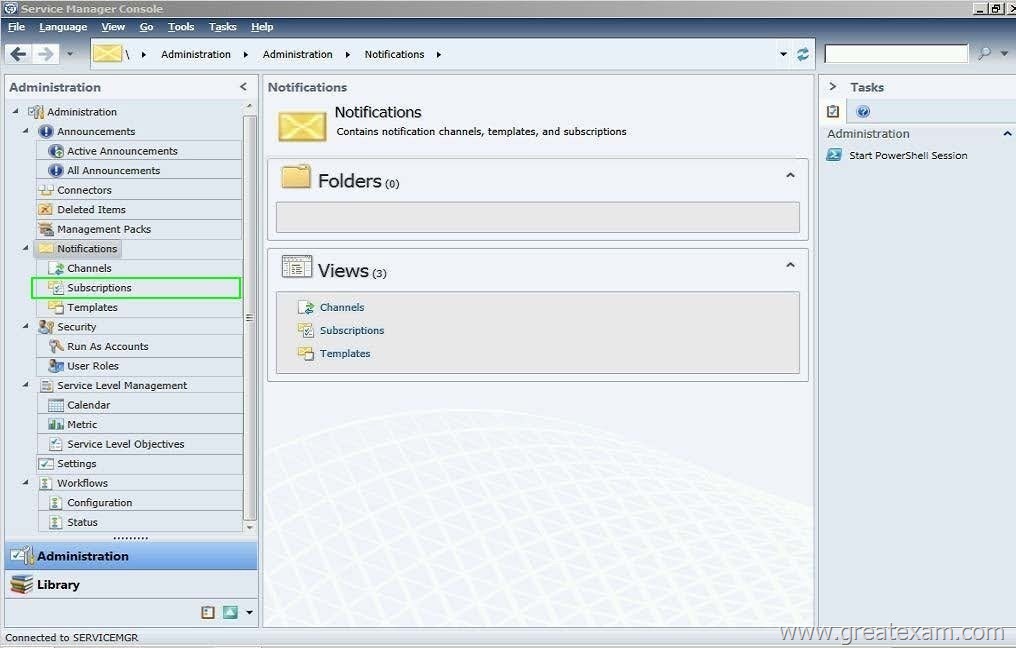
Explanation:
Service Manager uses notification subscriptions to automatically send notifications to selected recipients when a selected condition occurs.
Source: System Center 2012 Service Manager Console
My opinion it would be the Subscriptions menu as it gives access to the ‘Notification Subscription’ wizard.
http://technet.microsoft.com/en-us/library/ff460891.aspx
Before notifications are sent, first configure each notification channel, such as the settings for Simple Mail Transfer Protocol (SMTP). Notification messages are sent based on a notification template. Therefore, you will need to create a notification template.
You can then use the Notification Subscription wizard to subscribe a group of users to a notification that will be sent whenever the changes that you specify occur.
Finally, you can verify that a notification is sent by manually generating the change.
http://technet.microsoft.com/en-us/library/hh524284.aspx
– To create an email notification template and subscription – Step 4:
4.In the Administration pane, click Notifications, and then click Subscriptions.
In the Tasks pane, click Create Subscription, and then complete the Create E-Mail Notification Subscription Wizard.
QUESTION 35
Your company has a datacenter in Los Angeles that contains a private cloud.
The private cloud is managed by using a System Center 2012 Virtual Machine Manager (VMM) infrastructure.
You create a host group named HG1.
You move several Hyper-V hosts to HG1.
You plan to manage Windows updates for the hosts in HG1 by using VMM.
An administrator creates a baseline as shown in the exhibit. (Click the Exhibit button.)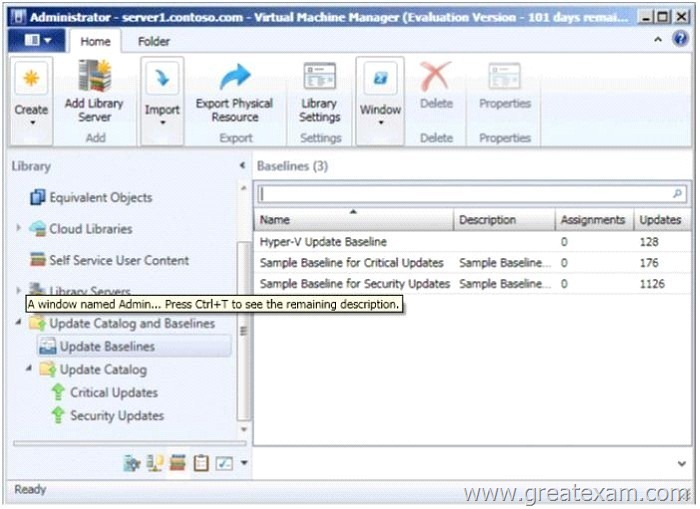
You discover that the updates defined in the baseline are not applied to the hosts in HG1.
You need to ensure that the required updates are deployed to the hosts in HG1.
What should you do?
A. Copy the required updates to the VMM library server.
B. Modify the properties of HG1.
C. Copy the Virtual Machine template to an alternate location.
D. Modify the properties of the baseline.
E. Synchronize the Windows Server Update Services (WSUS) server.
Answer: D
Explanation:
You can see from the exhibit, the baseline the administrator created is not applied.
To apply a baseline, you modify the properties of the baseline to select the hosts and groups.
Source information:
How to Configure Update Baselines in VMM
http://technet.microsoft.com/en-us/library/gg675110.aspx
Assign Computers to a Built-in Update Baseline VMM provides two sample built-in updates baselines that you can use to apply security updates and critical updates to the computers in your VMM environment. Before you can use a baseline, you must assign it to host groups, host clusters, or individual managed computers.
The following procedure explains how to assign computers to the sample security baseline.
To assign computers to a built-in update baseline
1. Open the Library workspace.
2. On the Library pane, expand Update Catalog and Baselines, and then click Update Baselines. The Baselines pane displays the two built-in baselines: Sample Baseline for Security Updates and Sample Baseline for Critical Updates.
3. On the Baselines pane, click Sample Baseline for Security Updates.
4. On the Home page, in the Properties group, click Properties. The Properties dialog box for the Sample Baseline for Security Updates opens.
Note:
On the left of the dialog box, click Updates to open the Updates page.
5. On the Updates page, optionally add or remove update baselines from the baselines that are listed. The Sample Baseline for Security Updates includes all security updates. To ensure that all security updates are remediated, do not remove any baselines.
6. Click Assignment Scope to open the Assignment Scope page and then, select host groups, host clusters, and computers to add to the baseline.
Computers are represented by the roles they perform in VMM. When you select a role, such as VMM server, all the roles that the computer performs in VMM are selected. For example, if your VMM management server is also a library server, selecting your VMM management server under VMM Server causes the same computer under Library Servers to be selected. To apply a baseline to all hosts, select the All Hosts root host group.
7. Click OK to save your changes.
QUESTION 36
Your role of Systems Administrator at ABC.com includes the management of the company’s private cloud.
The private cloud is hosted on an internal System Center 2012 infrastructure.
The network includes servers that run Windows Server 2008 R2 Hyper-V and are managed by servers running System Center 2012 – Virtual Machine Manager (VMM).
You are configuring a hardware profile in VMM.
The hardware profile will be used to create virtual machines configured for Windows Network Load Balancing.
In the Network Adapter Properties, you configure the network adapter to be connected to a logical network and to use a Static IP address from the Static IP Pool.
You now need to configure the MAC address options.
Which two of the following options should you configure? (Choose two).
A. You should select the option for a Dynamic MAC Address.
B. You should select the option for a Static MAC Address.
C. You should tick the Enable Spoofing of MAC Addresses checkbox.
D. You should clear the Enable Spoofing of MAC Addresses checkbox.
Answer: BC
Explanation:
In order for NLB service to function properly, it will assign all clustered NIC the same MAC address. It cannot do this if spoofing is disabled, so answer C is valid. Additionally, we want to make sure that once the MAC addresses are set by NLB, they don’t change, this means answer B is valid.
http://technet.microsoft.com/en-us/library/bb742455.aspx
http://blogs.technet.com/b/jhoward/archive/2009/05/21/new-in-hyper-v-windows-server-2008-r2-part-2-mac-spoofing.aspx (Since VMM is an abstraction to hyperv, we can assume hyperV NLB requirements are the same as VMM NLB requirements.)
QUESTION 37
Your company has a private cloud that is managed by using a System Center 2012 infrastructure. The network contains 50 virtual machines that run Windows 7.
Each virtual machine has an application named Appl.exe installed.
A new version of Appl.exe is released.
You need to identify which virtual machines have the outdated version of App1.exe installed.
What should you do?
A. From Operations Manager, create a monitor.
B. From Configuration Manager, deploy a Desired Configuration Management baseline.
C. From Service Manager, create a Virtual Machine Manager (VMM) connector.
D. From Virtual Machine Manager (VMM), deploy a service template.
Answer: B
Explanation:
Desired configuration management in Configuration Manager 2007 allows you to assess the compliance of computers with regard to a number of configurations, such as whether the correct Microsoft Windows operating system versions are installed and configured appropriately, whether all required applications are installed and configured correctly, whether optional applications are configured appropriately, and whether prohibited applications are installed.
Additionally, you can check for compliance with software updates and security settings.
http://technet.microsoft.com/en-us/library/bb680553.aspx
QUESTION 38
Your company has a private cloud that is managed by using a System Center 2012 infrastructure. You deploy Data Protection Manager (DPM) to a server named DPM1.
A server named Server1 has the Hyper-V server role installed and hosts a virtual machine named VM1.
From DPM1, you perform a full backup of Server1.
You discover that you are unable to restore individual files from VM1.
You need to ensure that you can restore individual files from VM1 by using the DPM Administrator console.
What should you do first?
A. On VM1, install Windows Server Backup.
B. On DPM1, attach the VHD of VM1.
C. On DPM1, install the Hyper-V server role.
D. On VM1, install the integration features.
Answer: C
Explanation:
In either case, DPM utilizes the Hyper-V VSS writer to synchronize block-level differences within the VHDs using a process called an “Express Full”, which identifies which blocks have changed in the entire VHD and then sends just the updated blocks or fragments. This provides a complete and consistent image of the virtual hard disk files on the DPM server or appliance.
DPM maintains up to 512 shadow copies of the full VHD set by storing only the block-level differences between any two images.
http://blogs.technet.com/b/bettertogether/archive/2010/11/16/why-dpm-2010-and-hyper-v-are-better-together.aspx
Credit to computer for finding this one
QUESTION 39
Your company has a private cloud that is managed by using a System Center 2012 infrastructure. The infrastructure contains multiple servers that have Data Protection Manager (DPM) installed. A DPM server named Server1 is running out of hard disk space.
You add additional physical hard disks to Server1.
You verify that the additional disks are available from the local Disk Management console.
You need to ensure that the additional disk space can be used to store DPM backups.
What should you do?
A. From the DPM Administrator console, click Refresh.
B. From the DPM Administrator console, click Disk Allocation.
C. From the DPM Administrator console, click Add.
D. From the DPM Administrator console, click Rescan.
Answer: C
Explanation:
To add disks to the storage pool.
In DPM Administrator Console, on the navigation bar, click Management, and then click the Disks tab. In the Actions pane, click Add.
The Add Disks to Storage Pool dialog box appears.
The Available disks section lists the disks that you can add to the storage pool.
Select one or more disks, click Add, and then click OK. Adding Disks to the Storage Pool
http://technet.microsoft.com/en-us/library/bb808852.aspx
QUESTION 40
Your company has a private cloud that is managed by using a System Center 2012 infrastructure. You deploy Data Protection Manager (DPM) to the private cloud.
You configured DPM to back up the following information on 20 servers that run Windows Server 2008 R2:
– Data volumes
– System state data
– Volume mount points
You discover that the system state backup fails on all of the servers.
You can verify that all other data is backed up successfully.
You need to ensure that the system state backup completes successfully on all of the servers. What should you do?
A. Install Windows Server Backup on each server.
B. Connect each server to a dedicated LUN.
C. Reinstall the DPM agent on each server.
D. Add each server to a dedicated protection group.
Answer: A
Explanation:
A system state backup uses the Windows Server Backup feature to take a snapshot of the system state and saves it locally to the server before moving it to the DPM server storage pool. Troubleshooting Data Protection Manager System State and Bare Metal Backup
http://blogs.technet.com/b/dpm/archive/2011/10/31/troubleshooting-data-protection-manager-system-state-andbare-metal-backup.aspx
QUESTION 41
Your company has a private cloud that is managed by using a System Center 2012 infrastructure. An administrator installs a new tape drive on a server that has Data Protection Manager (DPM) installed.
You discover that the tape drive is unavailable from the DPM Administrator console.
You verify that the tape drive is installed correctly on the DPM server.
You need to ensure that the tape drive is available from the DPM Administrator console.
What should you do from the DPM Administrator console?
A. From the Agents view, click Install.
B. From the Disks tab, click Add.
C. From the Protection view, click Tape.
D. From the Libraries view, click Rescan.
Answer: D
Explanation:
To configure tape libraries
In DPM Administrator Console, on the navigation bar click Management, and then click the Libraries tab.
In the Actions pane, click Rescan.
The Rescan operation might take several minutes to complete.
DPM will add any library jobs to the queue that began during the Rescan operation.
If a library job is already in progress when the Rescan operation begins, the Rescan operation will fail.
Configuring Tape Libraries
http://technet.microsoft.com/en-us/library/ff399665.aspx
QUESTION 42
Your company has a private cloud that is managed by using a System Center 2012 infrastructure. You install the servers shown in the following table.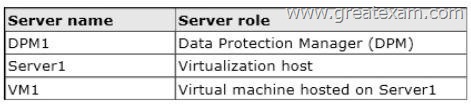
The company’s compliance department identifies the following tasks that must be performed:
– Back up individual files from VM1.
– Back up the configuration settings of VM1.
– Restore the configuration settings of VM1.
– Restore individual files from VM1 to an alternate location.
The compliance department administrators recommend installing the DPM agent on Server1, and then performing a full backup.
You need to identify which task is NOT met by the recommended solution.
Which task should you identify?
A. Restore individual files from VM1 to an alternate location.
B. Restore the configuration settings of VM1.
C. Back up the configuration settings of VM1.
D. Back up individual files from VM1.
Answer: B
Explanation:
In the event of disaster recovery, System Center Data Protection Manager (DPM) 2010 allows you to recover virtual machines as files to a network folder.
You can then copy those files to an alternate Hyper-V host server.
However, to start a virtual machine on an alternate Hyper-V host server, you have to manually create and configure the virtual machine using the recovered files. DPM 2010 supports alternate location recovery (ALR), which allows you to recover a Hyper-V virtual machine to an alternate stand-alone Hyper-V host or to a cluster. The recovered virtual machine is already registered and configured on an alternate Hyper-V host server.
http://technet.microsoft.com/en-us/library/ff634209.aspx
In a virtualized environment the issue is whether to backup from inside the guest or from the host. The latter provides “bare metal restore” of an entire VM where something’s gone catastrophically wrong with a VM (or the host) but in general it doesn’t provide granular restore of files / folders. DPM 2010 added Item Level Restore (ILR), allowing you to restore individual files or folders within a VM even though it had only been backed up from the host. But this capability was only available when DPM 2010 ran on physical hardware, if the DPM server itself was in a VM this capability was not available. DPM 2012 fixes this glitch and can now do ILR even when the DPM server is a VM.
http://4sysops.com/archives/dpm-2012-part-3-other-improvements/
QUESTION 43
System Center 2012 Configuration Manager uses site system roles to support operations at each site. Computers that host the Configuration Manager site are named site servers, and computers that host the other site system roles are named site system servers.
Site system servers within the same site communicate with each other by using which protocol?
A. SMB
B. HTTPS
C. HTTP
D. Any of these
Answer: D
Explanation:
Site system servers within the same site communicate with each other by using server message block (SMB), HTTP, or HTTPS, depending on the site configuration selections that you make. Because these communications are unmanaged and can occur at any time without network bandwidth control, review your available network bandwidth before you install site system servers and configure the site system roles.
https://technet.microsoft.com/en-us/library/gg712701.aspx#Planning_Intra_site_Com
QUESTION 44
The Network Access Account is used by client computers when they cannot use their local computer account to access content on distribution points.
For example, this applies to workgroup clients and computers from untrusted domains.
This account might also be used during operating system deployment when the computer installing the operating system does not yet have a computer account on the domain.
Which of the following is FALSE?
A. You can configure the Network Access Account on a central administration site.
B. You should not grant this account interactive logon rights
C. When Configuration Manager tries to use the computername$ account to download the content and it fails, it automatically tries the Network Access Account again, even if it has previously tried and failed.
D. The Network Access Account is never used as the security context to run programs, install software updates, or run task sequences; only for accessing resources on the network.
Answer: A
QUESTION 45
Application management in System Center 2012 Configuration Manager provides Configuration Manager administrative users and the users of Configuration Manager client devices with tools to manage applications in the enterprise.
Complete the missing term below:
A new client program, ___, provides a user-friendly interface that allows the user of a client computer to perform typical tasks to help manage software installed by Configuration Manager on their devices
A. Software Center
B. Application Catalog
C. Delta Discovery
D. Heatbeat Discovery
Answer: A
QUESTION 46
How many clients can be supported when SQL Server is installed on the same computer as the site server?
A. 100,000
B. 10,000
C. 150,000
D. 50,000
Answer: D
Explanation:
A child primary site that uses a remote installation of SQL Server cannot support more clients than is supported by the version of SQL Server that is in use at the central administration site, which can limit the total number of clients the hierarchy supports. The version of SQL Server that is used by a secondary site does not affect the number of clients that the primary site supports.
QUESTION 47
A primary site can support up to 10 management points.
However, when you increase the number of management points at a primary site, you do not increase the maximum number of clients that the site can support.
Instead, additional management points provide redundancy for communications from clients.
How many management points does a secondary site support?
A. 10
B. None
C. 5
D. 1
Answer: D
QUESTION 48
Daily recovery point size refers to the total size of changes made to protected data during a single day. It is roughly equivalent to the size of an incremental backup.
Retention range refers to the number of days for which you want to store recovery points of protected data on disk.
Complete the missing terms below:
For files, DPM can store a maximum of ___ recovery points for each volume included in a protection group, and it can create a maximum of ___ scheduled recovery points for each protection group each day.
A. 124, 16
B. 64, 8
C. 512, 64
D. 256, 32
Answer: B
Explanation:
The limit of 64 recovery points for files is a result of the limitations of the Volume Shadow Copy Service (VSS), which is necessary for the end-user recovery functionality of DPM.
The recovery point limit does not apply to application data.
QUESTION 49
Which term is described below:
A feature in Operations Manager that allows the collection of client application crash data to a single location on a management server, resulting in data that can then be analyzed by your company for patterns.
A. Operations Manager Connector Framework
B. Agentless Exception Monitoring
C. System Center Data Access service
D. Operations Manager Shell
Answer: B
QUESTION 50
Drag and Drop Questions
Your company has a private cloud that is managed by using a System Center 2012 infrastructure. The network contains an Orchestrator infrastructure and a Service Manager infrastructure.
You need to automate user account provisioning for the Self-Service Portal.
The solution must ensure that new user accounts are approved by a member of the human resources department.
You configure the Orchestrator connector.
Which five actions should you perform next? (To answer, move the appropriate actions from the list of actions to the answer area.)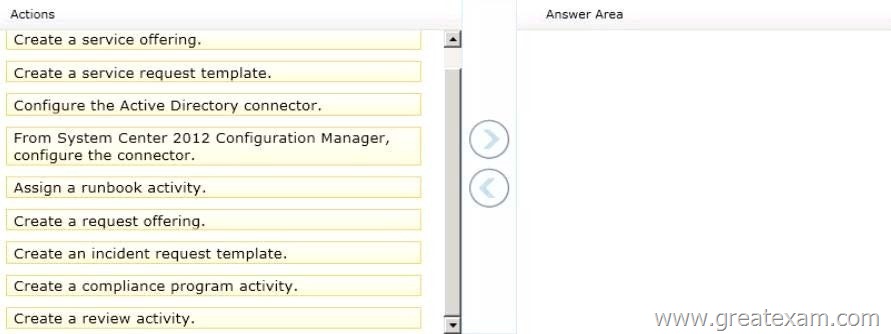
Answer: 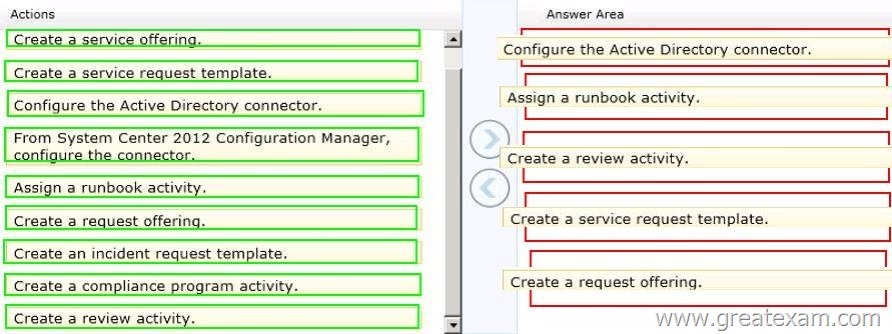
Explanation:
http://syscen.blogspot.com/2012/01/automating-new-user-creation-with-scsm.html
http://syscen.blogspot.com/2012/02/automating-new-user-creation-with-scsm.html
http://syscen.blogspot.com/2012/02/automating-new-user-creation-with-scsm_09.html
http://syscen.blogspot.com/2012/02/automating-new-user-creation-with-scsm_15.html
1. Create Runbook Automated Activity Template
2. Extend service request class
3. Create Service Request template using the new Class and include the Runbook Automated Activity Template.
4. Create the Service Request Offering.
If you want to prepare for 70-246 exam in shortest time, with minimum effort but for most effective result, you can use GreatExam 70-246 practice test which simulates the actual testing environment and allows you to focus on various sections of 70-246 exam. Best of luck!





